Georgia SoftWorks’ SSH Server and SSH Client provides a FIPS 140-2 compliant option for those entities with requirements to meet cryptographic module security standards to protect sensitive and valuable data.
What is FIPS 140-2?
FIPS 140-2 stands for Federal Information Processing Standards under Publication 140-2. It is the U.S government computer security standard used to approve cryptographic modules. FIPS certification standards are either mandated or recommended for use in federal government information technology systems. Their requirements not only cover the cryptographic modules themselves, but also their documentation and some aspects of the source code.
Does the GSW SSH Server meet the FIPS 140-2 Standards?
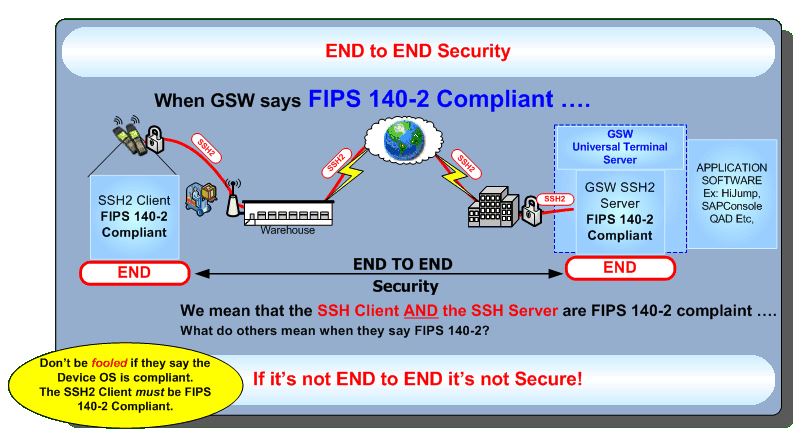
Yes! Under contract with the United States Military, GSW developed an End-to-End SSH FIPS 140-2 compliant solution (Client and Server) to meet their requirements. Now, Georgia SoftWorks is able to make this FIPS 140-2 compliant solution available commercially for other Federal and State agencies, as well as other private enterprises and institutions that need or desire government grade security requirements.
If I get the GSW FIPS 140-2 compliant SSH Server, how much does it cost to include the FIPS 140-2 compliant clients? I want to make sure it’s secure from start to finish.
The Georgia SoftWorks FIPS 140-2Compliant SSH Server includes the FIPS 140-2 compliant clients at NO EXTRA COST. Georgia SoftWorks will provide you true end-to-end security that you can count on. The GSW SSH Server with FIPS 140-2 compliance option provides both TRUE client and server compliance for organizations that must meet these high standards. If it’s not end-to-end, it’s NOT SECURE.
Where can I learn more about these security options?
You can view more information on the GSW SSH Server for Windows and its security measures here: http://www.georgiasoftworks.com/fips-140-compliant-ssh
You can also try the GSW FIPS 140-2 Compliant SSH Server for Windows free for 30 days!